Appearance
Sunsetting Legacy Applications with ACRA
Reducing Risk, Technical Debt, and Operational Overhead
Organisations retain legacy applications long after their operational relevance has ended, not by choice but by constraint. These systems are bound to end of life operating systems, unpatchable dependencies, fragmented ownership, and are often deployed as long lived, monolithic workloads running inside virtual machines. They remain online to meet regulatory, contractual, or historical obligations, even where safe change is no longer possible.
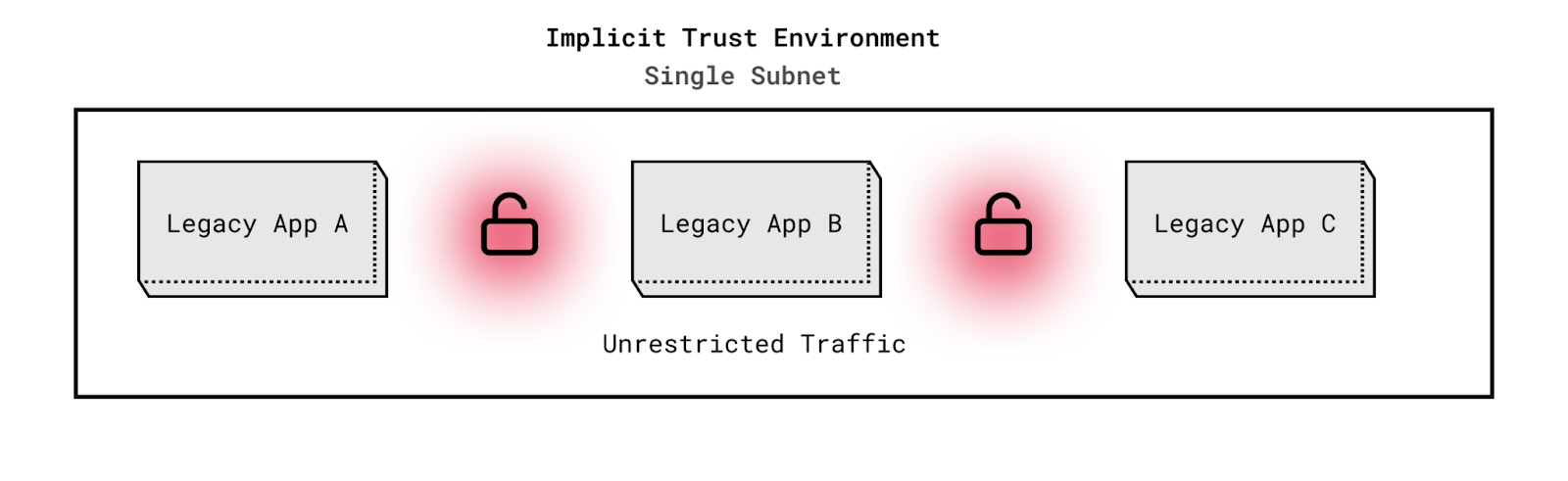
In many environments, these applications operate on flat networks built on implicit trust rather than enforced policy. Discovery, communication, and lateral movement are unrestricted by design. Visibility into workload interactions is limited, obscuring unauthorised data access and misuse of internal services. Without enforceable boundaries, identity based access controls, or workload attributable network telemetry, organisations cannot reliably distinguish legitimate activity from compromise or apply controls with precision. The result is elevated risk and sustained cost, including bespoke firewall rules, overlapping monitoring tooling, manual audits, extended support contracts, and disruptive incident response.
ACRA provides a structural correction. Legacy applications are deployed into segmented, policy enforced enclaves and brought under a shared Kubernetes based orchestration environment alongside modern services. Network access, service communication, and user permissions are denied by default and only allowed where explicit identity and access policies exist, enforced centrally by the platform rather than the application. Data is encrypted at rest by platform enforcement. Risk is reduced to an acceptable compliance posture, blast radius is constrained through enforced isolation and least privilege policy, and behaviour is observable and auditable by design. These controls are applied at the platform layer, replacing application specific compensating measures with standardised, enforceable defaults. This same platform foundation allows legacy and modern workloads, including both containerised services and virtual machine based systems, to operate side by side under a single control plane while inheriting the same identity, policy, and observability controls.
The Legacy Application Problem
Legacy applications commonly exhibit the following characteristics:
Have undocumented or poorly understood network behavior
Over time, institutional knowledge degrades, leaving teams unsure which external systems, ports, or protocols the application depends on, complicating monitoring, segmentation, and effective containment.Run on end-of-life operating systems with known and unknown vulnerabilities
These applications are often bound to operating systems or runtimes that no longer receive security updates, leaving publicly documented vulnerabilities unaddressed and exploitable. In many cases, organizations are forced to pay exorbitant extended support fees to operating system vendors in order to maintain minimal security coverage for platforms that should otherwise be retired.Cannot be easily patched or upgraded
Tight coupling to legacy dependencies, brittle integrations, or lack of source code ownership make patching risky or operationally infeasible, increasing reliance on compensating controls rather than remediation and further extending the lifecycle of unsupported platforms.Lack modern authentication, authorization, or encryption controls
Many legacy applications assume a trusted internal network. Access is often mediated by shared credentials, hard coded secrets, or network location rather than explicit identity. Least privilege cannot be enforced consistently, and access decisions are difficult to audit or attribute.Expose data without clear access boundaries
Databases, file systems, and shared storage are frequently reachable by any workload on the network. Data access is governed by proximity rather than intent, making it difficult to restrict access, demonstrate compliance, or prevent unauthorised data movement without invasive application changes.
In legacy environments, these applications typically run in systems that are difficult to change because they exist to support applications that cannot be easily modified or migrated, resulting in environments governed by implicit trust rather than explicitly enforced policy:
Workloads share a common, non isolated network plane
Infrastructure is deployed without enforced segmentation or default deny policy. Service discovery and east west communication are unrestricted by default, collapsing isolation boundaries and enabling lateral movement once a single workload is compromised.Controls are applied reactively at the application level
Firewalls and access rules are maintained per application rather than enforced consistently at the infrastructure layer. Over time, rules drift, exceptions accumulate, and enforcement becomes inconsistent and difficult to reason about.Visibility and attribution are limited
Network telemetry is typically reduced to IP addresses and ports. Teams lack workload level identity, policy context, and real time attribution, making it difficult to distinguish legitimate behaviour from misuse or compromise.Management and control surfaces are network reachable
Administrative interfaces, management APIs, and operational services often reside on the same network plane as application workloads. Once a legacy application is compromised, attackers can probe and target these control surfaces, increasing the risk of privilege escalation and environment wide impact.Outbound access is broadly unrestricted
Workloads are typically allowed to initiate outbound connections by default. This enables command and control traffic, data exfiltration, and interaction with external services without explicit approval or visibility at the workload level. In flat network environments, workloads operate without enforced segmentation, workload identity, or default deny policy. Once a single legacy application is compromised, attackers can move laterally across reachable services with minimal resistance. Detection and response are slow and disruptive because activity cannot be reliably attributed to specific workloads, identities, or access decisions. Isolating a single system often requires broad network changes, service interruption, or environment wide containment.
ACRA addresses these conditions by enforcing segmentation, identity bound communication policies, and workload attributable network visibility at the platform layer. Implicit trust is removed. Access becomes explicit, auditable, and enforceable by design.
Implicit Trust Networks vs Policy Enforced Environments
In environments without enforceable workload identity or explicit communication policy, access decisions are inferred from network reachability rather than governed by design. Flat or weakly segmented network topologies are a common implementation of this model, but the underlying issue is the absence of default deny enforcement and identity bound control. As a result, east west communication is broadly permitted, service interactions are difficult to attribute, and observability is limited to coarse network indicators rather than meaningful workload level context. Security outcomes depend on reactive measures rather than architectural constraint, increasing operational fragility over time.
Implicit Trust Environment Characteristics
- Network reachability substitutes for access control, permitting east west communication unless manually restricted
- Flat or weakly segmented network layouts reinforce implicit trust rather than enforce isolation
- Workloads lack strong, verifiable identity
- Observability is limited to coarse network indicators, preventing reliable attribution of traffic to workloads, identities, or policies
- Security posture relies on patching, perimeter defences, and manual exception handling
Policy Enforced Environment Characteristics
- Communication is denied by default and permitted only by explicit policy
- Access decisions are bound to workload and service identity
- Network topology does not determine trust boundaries
- East west traffic is constrained to declared, auditable paths
- Observability is workload attributable and policy aware by design
- Service interactions can be traced, logged, and reviewed with clear context
- Blast radius is limited through enforcement rather than assumption
ACRA enforces segmentation through policy rather than topology. Communication between workloads is denied by default and allowed only through explicit, identity bound rules applied at the platform layer. All service interactions are authenticated, authorised, and observable with workload level attribution. Network behaviour is continuously logged and auditable, providing clear evidence of allowed and denied interactions. Under compromise, east west movement is restricted to declared paths, containing impact to the affected enclave and preventing propagation across applications or environments.
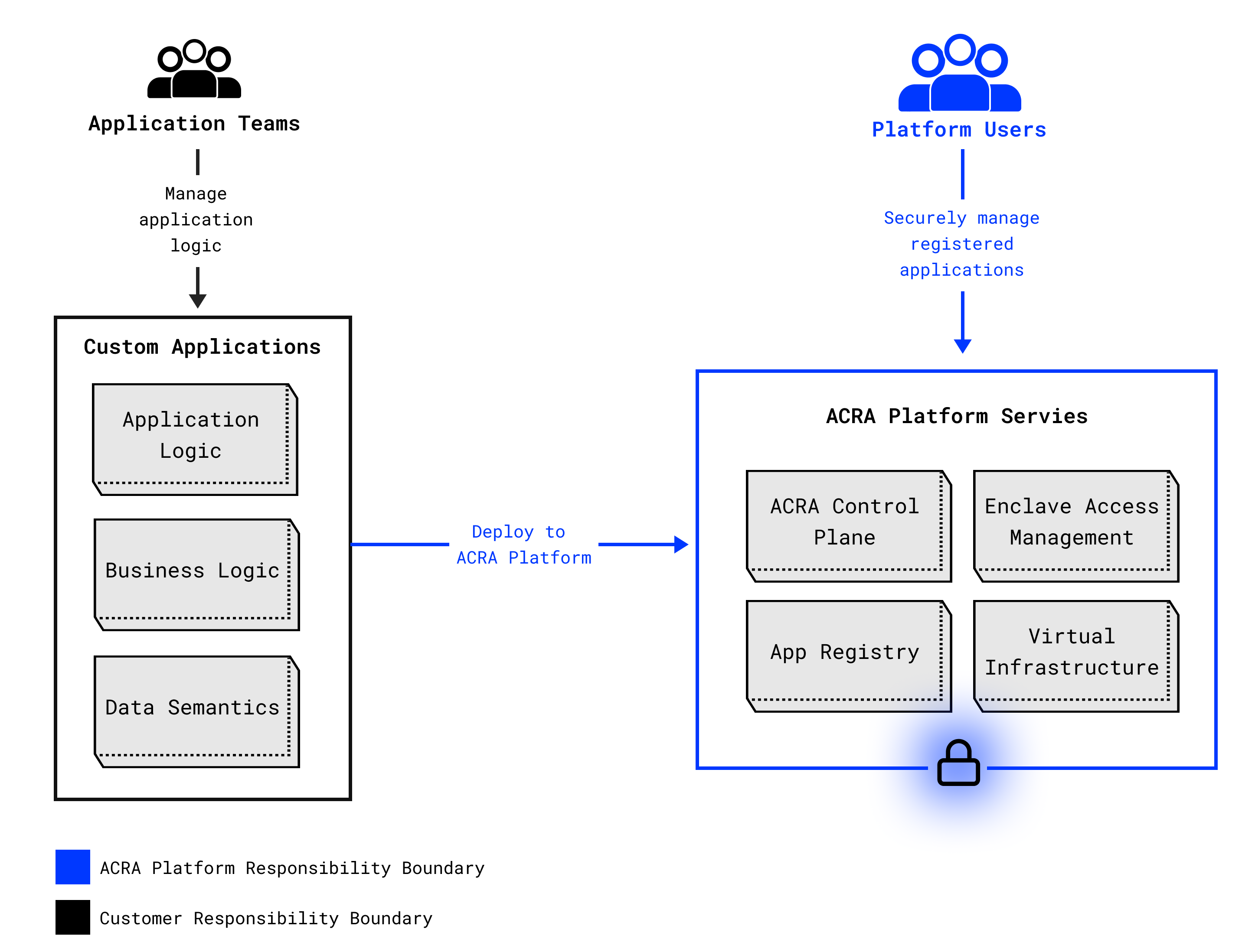
ACRA Approach to Legacy Application Sunsetting
ACRA enables organisations to move legacy applications out of implicit trust environments and into policy enforced virtual enclaves without modifying application code. Each enclave provides an isolated execution environment with explicitly controlled ingress and egress, allowing communication only along declared, policy enforced paths.
Service to service interactions are governed by declarative communication policies, while resource constraints, audit boundaries, and standardised observability across metrics, logs, and traces are enforced at the platform layer. Together, these controls ensure workloads remain contained, observable, and predictable. Because these controls apply uniformly at the platform layer, legacy workloads and newly developed services inherit the same identity, policy, and observability model. Modernisation can proceed incrementally, without carving out separate environments or relaxing controls during transition.
Network Segmentation and Policy Enforcement
ACRA enforces network control through explicit policy rather than assumed reachability. Communication is denied by default at every layer and only permitted where policy exists.
ACRA applies enforcement at two levels:
- Enclave level segmentation
- Communication between enclaves is denied by default
- All ingress and egress paths are explicitly declared and audited
- No implicit trust exists between environments
- Application level policy enforcement
- Layer 3 and Layer 4 transport traffic and Layer 7 application traffic are governed by strict default deny policies
- Service to service communication is permitted only where an explicit policy exists
- Policies are bound to verified workload identities rather than network location
- User initiated actions are constrained by least privilege, with permissions propagated and enforced across service boundaries
This model ensures that compromise does not translate into reach. Even if a legacy application is exploited, it cannot scan the network, discover peer services, establish unauthorised connections, or exfiltrate data beyond declared paths. Lateral movement is constrained by workload identity and least privilege policies, and impact is limited to the minimum scope required for the application to function.
Visibility Into Legacy Application Behaviour
One of the core challenges with legacy systems is understanding what they do at runtime. ACRA provides workload attributable visibility into network behaviour, including which services communicate, when interactions occur, and which ports and protocols are used. This makes unexpected dependency calls, anomalous outbound attempts, and policy violations visible early, even for applications that cannot be modified or instrumented.
Because communication is denied by default, unexpected connection attempts are blocked and recorded rather than merely observed. This turns unknown behaviour into high signal evidence and limits the ability of a compromised workload to propagate.
Underlying Technical Controls
ACRA enforces these guarantees at the platform layer rather than embedding logic in applications:
Default deny east west communication with identity bound service interaction
Service to service traffic is denied by default and permitted only where explicit policy exists. Workload identity and encryption in transit are enforced without application changes using Istio in Ambient mode [8].Observable Layer 3 and Layer 4 enforcement in the datapath
Network policy is enforced directly in the datapath with deny-by-default semantics, providing visibility into IPs, ports, protocols, and allow deny decisions. This is implemented using Cilium with eBPF [9].Encrypted, scalable persistent storage services
Stateful workloads use encrypted block volumes for databases and encrypted, S3-compatible object storage for files and artefacts. Storage encryption and replication are provided by Ceph (RBD and RGW) [10][11].Virtual machine workloads under platform enforcement
For monolithic or stateful legacy systems that cannot be containerised, ACRA supports virtual machine workloads managed alongside containers using KubeVirt. Virtual machines are treated as first class workloads and inherit the same network policies, identity enforcement, storage encryption, and audit controls as containerised services.
These controls ensure legacy workloads inherit isolation, identity based access boundaries, encryption in transit and at rest, and auditable network behaviour by default, without requiring code changes.
Reduced Technical Debt Through Compensating Controls
Traditional remediation for legacy systems relies on patching, rewriting, or replacing applications. These approaches are costly, slow, and often impractical for systems bound by operational, regulatory, or contractual constraints.
ACRA provides compensating controls through enforced isolation, explicit policy, and workload level visibility that reduce security risk to an acceptable compliance posture without modifying legacy code. By shifting control to the platform layer, organisations replace application specific exceptions and bespoke firewall rules with standardised, enforceable defaults. This reduces reliance on specialised monitoring stacks, lowers ongoing risk mitigation spend, and allows re-architecture efforts to proceed on a controlled timeline rather than under pressure. This enables teams to decompose or replace legacy components incrementally, while the original system continues operating within enforced boundaries.
The result is not the elimination of legacy systems, but the containment of their risk. Technical debt stops accumulating, and the operational overhead required to manage it is reduced by design.
Compliance and Auditability
ACRA records and audits network access decisions, identity based permission grants, and workload level interactions, producing an attributable record of how access is enforced and how legacy workloads behave at runtime. Both allowed and denied actions are logged with policy context, providing evidence suitable for security monitoring, incident response, and compliance review without requiring changes to legacy code. These guarantees persist during periods of change, ensuring that legacy and replacement workloads remain subject to the same access controls, audit evidence, and data handling requirements throughout transition.
This produces a defensible compliance posture for unmodifiable legacy systems. Enforcement is explicit, decisions are reviewable, and access can be demonstrated rather than inferred. The platform supports regulated environments where auditability, accountability, and data control are mandatory, including requirements for data residency and sovereignty.
Outcome: Controlled Legacy Continuity Without Rewrites
Legacy systems persist because they cannot be removed safely or quickly. Regulatory constraints, operational dependencies, and architectural coupling make wholesale rewrites impractical in most environments. The risk is not their continued operation, but the conditions under which they are forced to operate.
ACRA changes those conditions.
By placing legacy workloads into isolated, policy enforced enclaves, organisations replace implicit trust with explicit control. Legacy systems are removed from shared network planes, denied unauthorised lateral reach, and governed through identity based access controls and auditable policy enforcement. These guarantees are applied at the platform layer, without modifying application code.
The outcome is a controlled operating state rather than an unmanaged exception:
- Security exposure is bounded, measurable, and attributable
- Compromise is contained to explicitly permitted interactions
- Audit and compliance posture is enforced by architecture, not procedure
- Operational effort shifts from reactive mitigation to repeatable control
Within this model, legacy and modern workloads can coexist under a single execution and governance plane. Existing systems continue to run in constrained enclaves while new components or replacements are developed alongside them, subject to the same identity, policy, and observability controls. Modernisation becomes incremental and reversible rather than disruptive.
Legacy systems continue operating. Modern systems are introduced deliberately. Risk remains contained throughout.
This is not a rewrite strategy. It is a control strategy that allows organisations to extend the service life of critical systems while modernising on their own terms, without carrying uncontrolled exposure or operational fragility.
Conclusion
Legacy systems do not need to be trusted in order to remain operational. They need to be constrained by design, observable in practice, and governed explicitly.
ACRA provides a controlled execution environment where legacy workloads operate under enforced identity, policy, and audit boundaries. By replacing implicit trust with platform level enforcement, organisations reduce risk, stabilise compliance posture, and contain operational exposure without rewriting application code. Legacy systems continue to run, but no longer dictate the security or architectural limits of the environment in which future systems are built, regardless of execution format.
References:
- [1]: L3 is the network layer – this manages network addressing and routing to move data between networks. For example, IP is a layer 3 protocol.
- [2]: L4 is the transport layer – it focuses on managing end-to-end communication, flow control, and error correction for TCP and UDP protocols.
- [3]: L7 is the application layer – this is where the user-facing application runs and operates.
- [4] Cilium Network Policy Enforcement
- [5] Istio Service Identity and Mutual TLS Auth
- [6] Encrypted Block Storage (RBD)
- [7] Encrypted Object Storage (RGW)
- [8] Istio Ambient Mode
- [9] Cilium Network Policy
- [10] Ceph RBD
- [11] Ceph RGW